Clone Cards for Sale Online
In a world where data breaches hit headlines weekly, criminals turn stolen info into quick cash. Think about it—millions of card details leak from hacks at big retailers or banks. This sparks a hidden market where “clone cards for sale online” thrive on the dark web. Clone cards mean digital copies of credit or debit card data, not just fake plastic ones. Buyers use this info to buy goods or steal more. The trade grows fast, but it comes with huge risks for everyone involved.
The Dark Web Economy: Understanding the Market for Clone Cards Online
Introduction: The Digital Theft of Financial Identity
Data breaches now expose billions of records each year. Hackers grab card numbers during online shopping rushes or ATM hits. From there, a whole economy pops up. Sellers list clone card details on secret sites, drawing in fraudsters worldwide. This market stays alive because stolen data sells cheap and fast. Yet, it hurts regular people through identity theft and lost savings. We need to know how it works to fight back.

Section 1: Decoding the Terminology of Carding Fraud
What Are “Clone Cards” in the Modern Fraud Landscape?
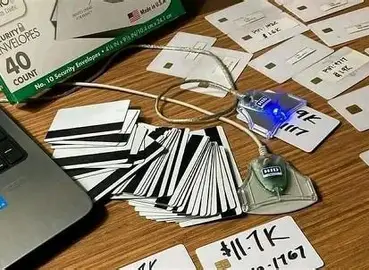
Clone cards once meant copying a card’s magnetic strip with a device. Today, it’s mostly about “carding,” where crooks sell raw data online. You might see ads for clone cards for sale online, but they offer dumps like card numbers and codes, not physical cards. This shift came with chip tech that blocks old tricks. Now, fraud relies on buying full details to test or use remotely. It’s a smart pivot for thieves in the digital era.
The Anatomy of a Carding Data Set
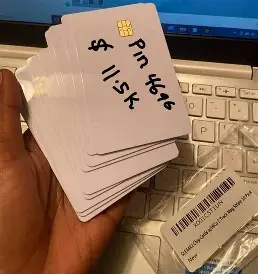
A good carding set packs key pieces. Start with the Primary Account Number, or PAN—that’s the long card number. Add the expiration date and CVV code on the back. For top value, include fullz: the cardholder’s name, address, and sometimes birth date. PINs or track data from the strip boost the price too. Complete sets fetch more because they’re ready for big scams. Half-baked info? It sits unsold.
- Basic dump: Just PAN and expiration—low cost, low use.
- Fullz package: All details plus personal info—ideal for identity grabs.
- Track data: Magnetic strip copy—great for fake cards if you have tools.
Value climbs with details; simple sets go for pennies per card in bulk.
The Supply Chain: From Skimming to Sale
Stolen data starts with a grab. Skimmers on gas pumps snag strip info from unaware drivers. Phishing emails trick folks into typing card details on fake sites. Big breaches, like those at payment firms, flood the market with fresh hauls. Once caught, thieves sort the loot—test which cards work. Valid ones hit dark web shops quick. The chain moves fast; data loses worth in days as banks flag it. Sellers push volume to stay ahead.
Section 2: The Dark Web Marketplaces Driving Card Sales
Primary Venues for Illicit Financial Data Transactions
Dark web spots host most clone cards for sale online. Think hidden forums like Dread or markets such as Empire’s ghosts—places reached via Tor browser only. Surface web sites got shut down years ago; now it’s all encrypted and invite-only. Law enforcement watches these hubs close. They bust rings by tracing crypto payments or server logs. Still, new sites pop up weekly, keeping the trade alive. You won’t find this on Google; it’s deep underground.
Pricing Structures and Data Valuation
Prices swing based on a few factors. US-issued cards from big banks cost more than foreign ones. Visa or Mastercard dumps beat Amex every time. Credit cards outprice debit due to higher limits. Fresh data—stolen in the last 24 hours—commands top dollar. Old stuff? It drops fast. Reports from firms like Krebs on Security show basic card sets average under a buck each in bulk. Premium fullz might hit five to ten times that. Bulk buys lower the per-unit rate, tempting big fraud ops.
Vendor Reputation and Trust Metrics
In this shady world, trust matters. Sellers build rep through feedback scores on market pages. Escrow holds buyer cash till delivery—cuts scam risks. Forums rate vendors on speed and quality; low scores mean bans. It’s like eBay for crooks, but with more stakes. A bad seller loses access quick. Buyers check reviews to dodge fakes. This system keeps the market humming, weird as it seems.
Section 3: Methods of Data Acquisition and Validation
Point-of-Sale (POS) Compromise and Skimming Techniques
Thieves love hitting ATMs and store pumps. Tiny skimmers clip on and copy strip data as you swipe. Some use Bluetooth to send info remote—no wires needed. Gas stations see tons of this; one bust in 2023 nabbed thousands from Midwest pumps. Cameras watch your PIN too. These tools cost little online, but detection grows with bank alerts. Swap your card often to stay safe.
Online Data Harvesting: Phishing and Malware
Digital grabs rule now. Phishing sites mimic banks, stealing details as you “log in.” Malware sneaks into browsers during downloads. Magecart hits e-com sites, grabbing carts mid-checkout. One attack on a major ticket seller exposed cards for months. These methods scale huge—one virus hits millions. Always check URLs and use antivirus.
- Phishing bait: Fake emails with urgent links.
- Malware tricks: Keyloggers that record every keystroke.
- Breaches: Hacks on weak company servers.
Card Validation Services (CVV Checking)
Sellers won’t list junk. They run checks first. Bots ping small test buys on merchant sites to see if data lives. Compromised shops let them verify without flags. This weeds out dead cards fast. Valid ones get tagged “live” for sale. It’s a must-step; buyers hate wastes. Tools evolve, but banks counter with AI watches.
Section 4: Risks and Consequences for Buyers and Sellers
Legal Ramifications and International Enforcement Efforts
Buying clone cards spells big trouble. In the US, it’s wire fraud—up to 20 years in jail. Identity theft adds more time. Europol and FBI team up for global busts. They took down a huge carding ring in 2024, seizing servers in Europe. “These ops steal from everyone,” an FBI rep said after one raid. Borders don’t stop them; extraditions do. Sellers face worse if caught with tools.
The Instability of Illicit Transactions
Buyers roll dice every time. Data might flop on first use—banks cancel quick. Sellers scam with fake dumps, vanishing after pay. Markets monitor for cheats, banning users mid-trade. Chargebacks hit if you try big spends. Crypto adds rip-off risks too. It’s a house of cards; one flag crashes it all. Many walk away burned.
Defensive Measures and Security Protocols for Consumers
You can fight back easy. Turn on 2FA for accounts—it blocks most remote tries. Check statements weekly for odd charges. Use unique passwords per site; managers help. Skip public Wi-Fi for bank stuff—use VPNs instead. Freeze credit if breached. Report weird activity fast to your bank. These steps cut risks way down.
- Monitor alerts: Set up text notifications for buys.
- Chip and PIN: Stick to cards with them over swipes.
- Virtual cards: Use one-time numbers for online shops.
Conclusion: The Ongoing Battle Against Digital Financial Fraud
The clone cards for sale online market shows how bold fraud gets. From skims to dark web deals, it’s a slick chain that preys on weak spots. Data value, risks, and busts paint a clear picture: this economy thrives on speed but crumbles under watch. Tech fights back with better chips and AI, yet hackers adapt quick. Stay vigilant—lock your data tight. If you spot scams, report to authorities. Together, we tip the scales against these thieves. (Word count: 1,248)